Products

- Products
- Cyber Drill System Notice: Undefined offset: 3 in /home/host/stealien/www/html/_skin/layout/inc_navigation_middle.php on line 86
Cyber Drill System
Home -> Products -> Cyber Drill System
Cyber Drill System


- Cyber
Drill System - Cyber drill system provides interactive training environment for cyber-attacks/defenses by simulating cyber-attack environments and scenarios, such as Web and Reversing.
Main Functions
-
-
Develop and provide contents
-
- Provides various contents including web, App, IoT, system, network, and malicious codes, in both one-way and two-way formats
- Clients can access Cyber Drill System and download cyberattack education contents and study the cyber-attack scenarios
- STEALIEN is capable of conducting further researches in areas of cyber-attacks which the clients require
-
-
-
Contents management
-
- Can edit contents’ name, description, and total score
- Can edit contents’ settings
-
-
-
Management Functions
-
- The administrator can manage the system with various menus, such as manage conversations, teams, users, user progression status, etc
- The administrator can manage the entire system
-
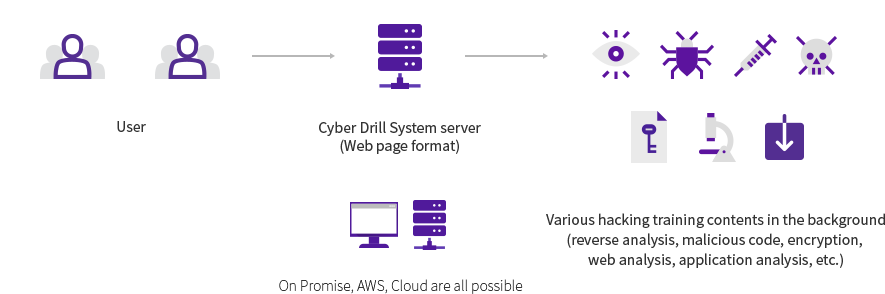
Product Application Method
- Cyber drill system can be accessed from the client server, after the system module installation, or the STEALIEN server
- Cyber drill system is accessed through webpage after its installation
- Clients can access the webpage to consume contents or utilize the administrator mode
Features
- Frequent content upgrades
-
- Provides frequent updates on the system contents with the 0-day vulnerabilities discovered by the STEALIEN technology research lab
- Incorporates hacking scenarios established during the mock hacking into the system contents
- Acquire Practical Capabilities
-
- Acquire practical capabilities through hacking practices
- Acquire attack/defense ability to respond to actual hacking attacks through attack/defense training
- Self-evaluation of the security of internal systems is possible based on acquired skills
- Identify the Trends of the Latest Technology
-
- Acquire the latest hacking skills similar to ransomware in training contents
- Continuous follow-up on new hacking technologies